ISO 27001 Certification: 4 Critical First Steps
ISO 27001 is a highly regarded and globally recognized Information Security Standard that can be applied to virtually any type or size of business. The ISO 27001 standard lays out the requirements for establishing, implementing, maintaining and continually improving an Information Security Management System (ISMS) that meets your business needs.
In contrast to other Information Security Standards, the concept of the ISMS is a unique feature of the ISO 27001 construct. Most Information Security Standards are focused on compliance with a specific set of defined security controls focused on a well-defined dataset. ISO 27001 certification is focused on setting up a comprehensive system within your organization, focused on the management of information security.
The flexibility with the ISMS approach is one of the key reasons why ISO 27001 is so widely used around the world. In addition, the Standard is fully risk-based in responding to your specific business needs, and not driven by the presence of any particular data class.
Defining and setting up the Information Security Management System requires thinking through many questions relevant to your business. The first question that should be asked though is: what parts of your business do you want to include in the Scope of the ISMS? Put another way, how do you want to draw the virtual box around your organization, within which you will manage information security according to your security rules?
A specific definition of the Scope of the ISMS is critical and mandatory for certification to the ISO 27001 standard. Many other standards may impose the scope for you because of the presence of financial or health related information. While these considerations may be factors in your decision, under ISO 27001 you get to define the scope.
So how do you arrive at the scope of your ISMS? Fortunately, the process and approach are laid out early in the ISO/IEC 27001:2013 Standard, in Clause 4: Context of the Organization.
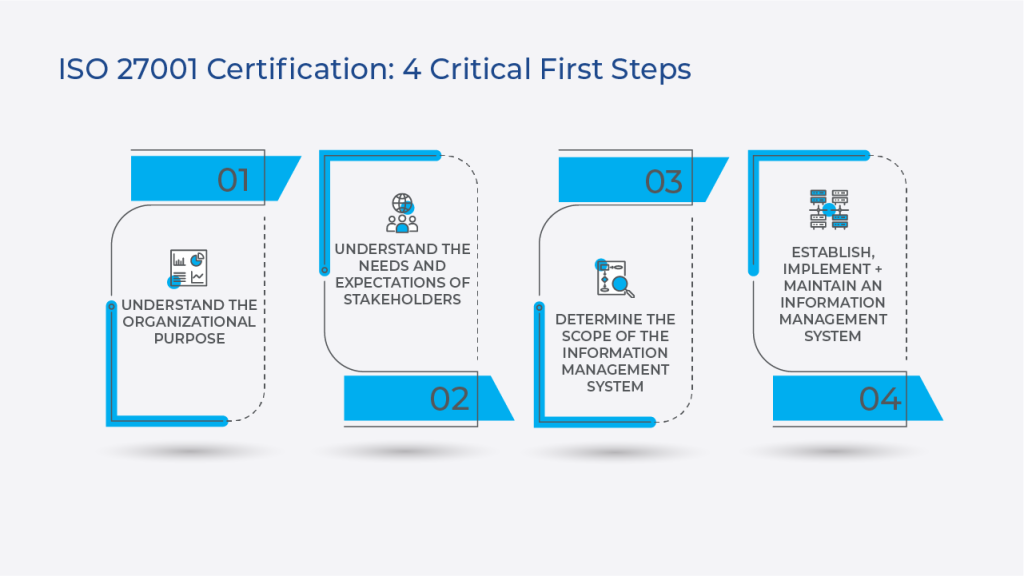
There are 4 sub-components of the Clause 4:

Understand the Organizational Purpose
Within section 4.1, you would figure through the various internal and external issues to be considered as relevant to the question of Information Security within your business. The Standard indicates that you could use ISO 31000 section 5.3 as a guide for this, but it is not mandatory. Examples of external issues could be cultural factors such as the social, political, legal or regulatory concerns. Examples of internal issues could be company governance, organizational structure and roles and accountabilities.

Understand the Needs and Expectations of Stakeholders
Section 4.2 is where you think through and document the various stakeholders and parties interested in the outcome of the heightened focus on Information Security in the company. Chief among these are usually top management, investors and customers who are concerned about how you are securing their data. Once identified, you should understand and document the requirements of these stakeholders as it relates to information security.

Determine the Scope of the Information Security Management System
Section 4.3, you are going to take account of the information you have considered in 4.1 and 4.2 to draw the broad boundaries around the parts of your business you feel should be included in the scope of the ISMS. To add further clarity on those boundaries though, you must also think through any interfaces and dependencies between activities performed by your organization, and those that are performed by other entities. For example, are you using a data center or cloud service provider, and in that relationship, who is responsible for what?

Establish, Implement and Maintain an Information Security Management System
This final part in 4.4 is, having defined the scope of the ISMS around your business, or part of it, you must then establish, implement, maintain and continually improve the information security management system, in accordance with all the other Clauses 4 through 10 in the Standard. All of these are mandatory for certification.
We would recommend that all of the above should be documented for the auditors, especially the Scope in 4.3, in detail.
One last point: As you launch yourself on this journey, just keep in mind the focus and objective is the security of the information that is important to your particular business. In other words, it’s all about the data.
Please reach out to us at connect@compliancepoint.com if you have any questions about ISO 27001. CompliancePoint’s ISO experts can walk you through the certification process and help you achieve your goals.
Finding a credible expert with the appropriate background, expertise, and credentials can be difficult. CompliancePoint is here to help.






