Scoping Your HITRUST Assessment
One of the advantages of the HITRUST Common Security Framework (CSF) is that it is scalable to the organization seeking certification. The scoping of the assessment determines which controls will be applicable to your assessment. As a result, it is very important that an organization properly scope their environment prior to beginning either a Self-Assessment or Validated Assessment.
There are several factors which impact your controls:
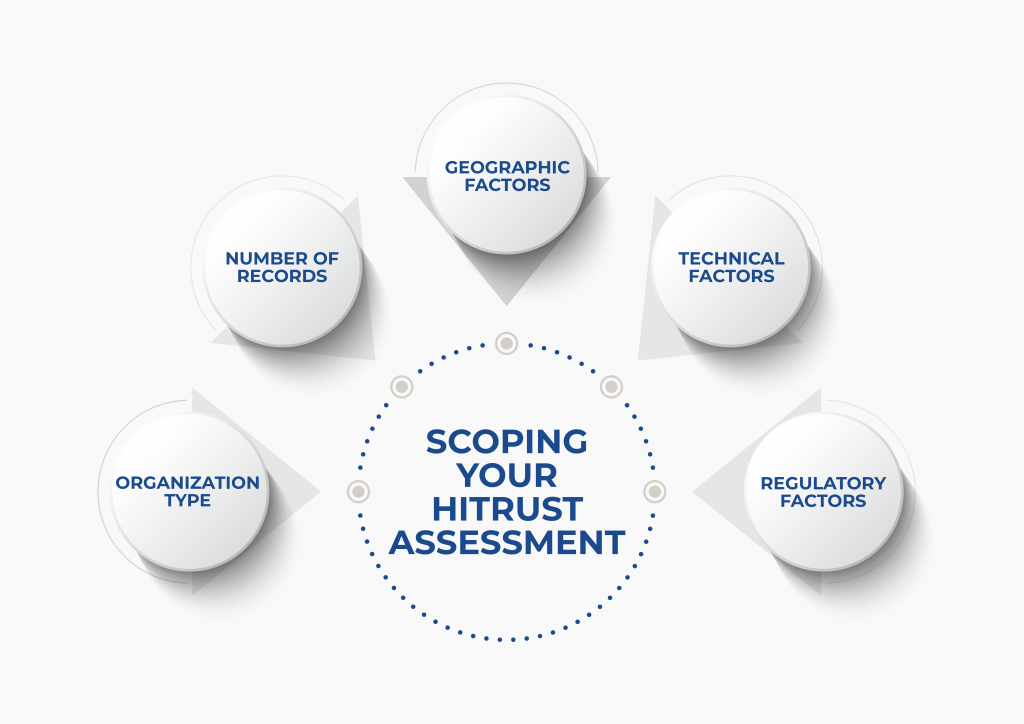
- Organization Type: The Organization Type is your legal classification. It includes payors, providers, and service providers. Most business associates seeking HITRUST certification would be considered Service Providers (Information Technology).
- Number of Records: This is
the single most important factor in determining how many controls you will
have. Generally, for organizations working in healthcare, a record would be
considered the information related to one person. For other organizations, the
records might be the number of sensitive records received or transmitted. HITRUST
has three levels for records:
- Less than 10 million
- Between 10 million and 60 million
- Over 60 million
- Geographic Factors: The geographic factors drive the assignment of controls based on the risk involved. An organization can either be one state, multi-state, or offshore. HITRUST considers anything outside the United States, including Canada or Mexico, to be offshore.
- Technical Factors: There
are several Technical Factors that impact the controls assigned to an
assessment. The factors below are particularly significant to the application
of controls to your organizations CSF framework:
- Is the system accessible from the internet? If users access the system via the internet this is applicable. This applies even if the access is behind a firewall accessible only after first establishing access to an internal domain (e.gl, VPN).
- Is the scoped system accessible by third party personnel? If the system is accessible by anyone outside of your organization, this would be applicable. The response to this should be “yes” if it is theoretically possible that the third-party could have access, even if they don’t routinely use this access, such as with data centers and cloud providers. Your customers would not be considered a third-party.
- Number of interfaces to other systems. This is the number of connections a system or application has with other systems to share data, where the other system is outside the scope of the assessment.
- Number of users of the system. The number of users who have access to the system.
- Number of transactions per day. How many transactions per day based on your average over a year. A transaction is defined as a discrete event between a user and the system.
- Does the organization allow personally-owned (BYOD) devices to connect to scoped organizational assets? If your employees use personal cellphones or laptops for any purpose, this would be applicable.
- Does the organization perform information systems development (either in-house or outsourced) for any scoped system, system service, or system component? If your organization creates, tests, constructs and/or introduces new systems, including but not limited to, application, interface, database and API development, this would be applicable.
- Does the organization use any part of the scoped systems, system components, or system services to sell goods and/or services? If your system sells services or takes payment, this would generally be applicable.
- Does the organization allow the use of electronic signatures to provide legally binding consent within the scoped environment? If you use electronic signatures within your scoped environment, this is applicable. It is generally not applicable if you are using products such as DocuSign for legal documents.
- Regulatory Factors: HITRUST has several regulatory factors you can choose to include in your assessment. These include FISMA, MARS-E, CMMC, GDPR, CCPA FedRAMP, PCI and others. Additionally, most organizations working with protected health information will be subject to HIPAA. HITRUST allows you to indicate which of the HIPAA rules would be applicable for your assessment (Privacy, Security, Breach Notification)
Properly scoping your environment is key to getting an accurate MyCSF framework. HITRUST will confirm your scope before proceeding with their review of the assessment, and should they identify discrepancies in your scope, it could result in controls being added that you did not expect.
CompliancePoint has experienced assessors who have worked with both providers and business associates to achieve HITRUST certification. If you are interested in how we can help, please reach out to us at connect@compliancepoint.com.
Finding a credible expert with the appropriate background, expertise, and credentials can be difficult. CompliancePoint is here to help.






